Many premium vehicles on sale today now contain more software than a commercial aircraft, in some cases exceeding 100 million lines of code. The number of electronic control units (ECUs) in modern cars has soared, bringing swathes of new functionalities to consumers. Worryingly, it has also created opportunities for hackers to tamper with critical driving functions, with potentially dire consequences.
In an effort to reverse the trend, the industry has embarked on a strategy to reduce the number of ECUs within new vehicles and cut back on unnecessary coding. It has seen automakers and suppliers alike place cyber security as a top priority moving forward. Indeed, while California-based Green Hills Software (GHS) has its roots in the aerospace and defence sectors, automotive has quickly become the company’s largest market segment.
Software overload
Software currently dominates the rhetoric within automotive as the introduction of connected and automated features ramps up. ECUs have been added at will to support these technologies, but it has raised concern within the cyber security community. “Some people would say the trend was out of control,” said Joe Fabbre, Director of Platform Solutions at GHS. “In recent years, manufacturers would add another ECU every time a new function was introduced to a vehicle.”
A similar trend can be seen with connectivity. In the cockpit, digital dashes are fast becoming the norm in upmarket models—consider Audi’s Virtual Cockpit and the Peugeot i-Cockpit, for example. “There has been a rush to get systems internet-connected in order to provide additional services. At the same time, self-driving computers have also arrived,” said Fabbre. With a mix of safety-critical and entertainment-focussed software now running alongside each other, vehicles have become increasingly vulnerable. “Not enough thought has been put into the security architecture of the overall system. Luckily, we have not seen any malicious hacks in the wild, but researchers have proven that it is possible to perform remote attacks on these connected computers that now reside in cars.”
The risks became acutely apparent following one of the most high profile connected car hacks to date. In July 2015, a pair of researchers—now working at General Motors’ Cruise Automation unit—took control of a Jeep Cherokee remotely. A Wired journalist behind the wheel was left at their mercy, with all critical driving controls under their command. Later in 2016, the same hackers returned, this time using a laptop plugged directly into the vehicle’s CAN bus to control the vehicle. Cyber security has subsequently become a key consideration for manufacturers, and not just an afterthought. “There was a definite knee-jerk reaction from the industry,” recalled Fabbre. “Our phones started ringing far more frequently.”
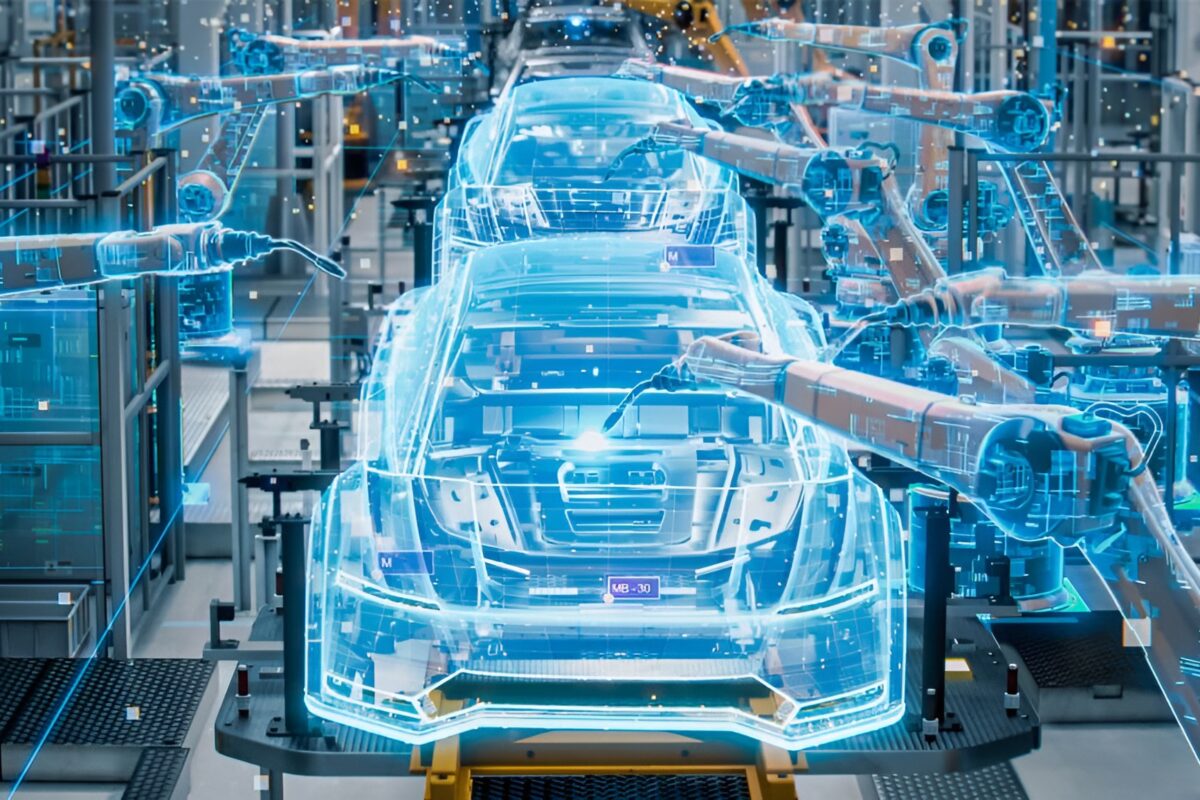
To compartmentalise mission critical software and cut back on physical computers, multiple ECUs are now being consolidated into single, more powerful processors. A similar shift took place in the aviation space more than a decade ago, with GHS seeing notable demand for its flagship real-time operating system ‘INTEGRITY’ at the time. The solution has since extended into the automotive space.
“It is far easier to secure those systems if there is an underlying software component to keep applications separate and ensure they cannot interfere with each other,” explained Fabbre. “It is not only critical to the overall safety of a system, but also security. Almost all security exploits occur when a hacker figures out how to take advantage of bugs in the software.”
More code, more problems?
With an eye to achieving high scale at high speed, off-the-shelf coding is often favoured to save time and effort. Moving forward, the automotive industry may need to reconsider its thirst for complex code; vehicles are bloating as a result of overly dense software, and the attack surface for hackers is growing almost daily.
Simple mathematics illustrates the problem. On average, anywhere between one and 25 defects can be found per 1,000 lines of code, according to the publication Code complete: A Practical Handbook of Software Construction. In addition, Fabbre estimates that over the course of five years, roughly 0.05 vulnerabilities are discovered per 1,000 lines of code. For a vehicle that contains 50 million lines of code, this implies that 2,500 vulnerabilities will be discovered on the platform over five years.
These are concerning figures when considering that the automotive industry has somewhat overloaded on software. For example, Fabbre recalls one task where GHS was required to write a program that activates a rear-view camera and sends the video feed to an infotainment screen. Initially, GHS had been given a program that contained a staggering 100,000 lines of code to perform that task. GHS developers managed to slash that to just 900 lines. “All we wanted to do was turn the camera on and put those pixels on the screen—surely we didn’t need 100,000 lines of code to do that,” he said. “It is safety critical, so we only need the bare minimum.”
Pure and simple
The underlying challenge is that numerous functions in the vehicle rely on software today, but often carry additional lines of unnecessary code. Cutting out the excess and ensuring software is as lean as possible would be a prudent approach for the automotive industry, but it is no mean feat. “There is no question in my mind that the complexity of code can be reduced,” said Fabbre, “but it’s not easy.”
Many engineers today leverage software libraries where functions can simply be downloaded with a click. Development time can be slashed, but they inadvertently end up with extra code that is surplus to requirements. “When most people sit down to write software, the code is overly complex. Taking a critical approach and carving it down to its simplest and most elegant form is a skill that takes many years of practice and experience,” concluded Fabbre. “At Green Hills, we really focus on reducing complexity. This keeps the software simple and ultimately means it can be evaluated for security properties. In the long term, I believe this is how we will solve the security problem with cars, because this complexity is the killer.”