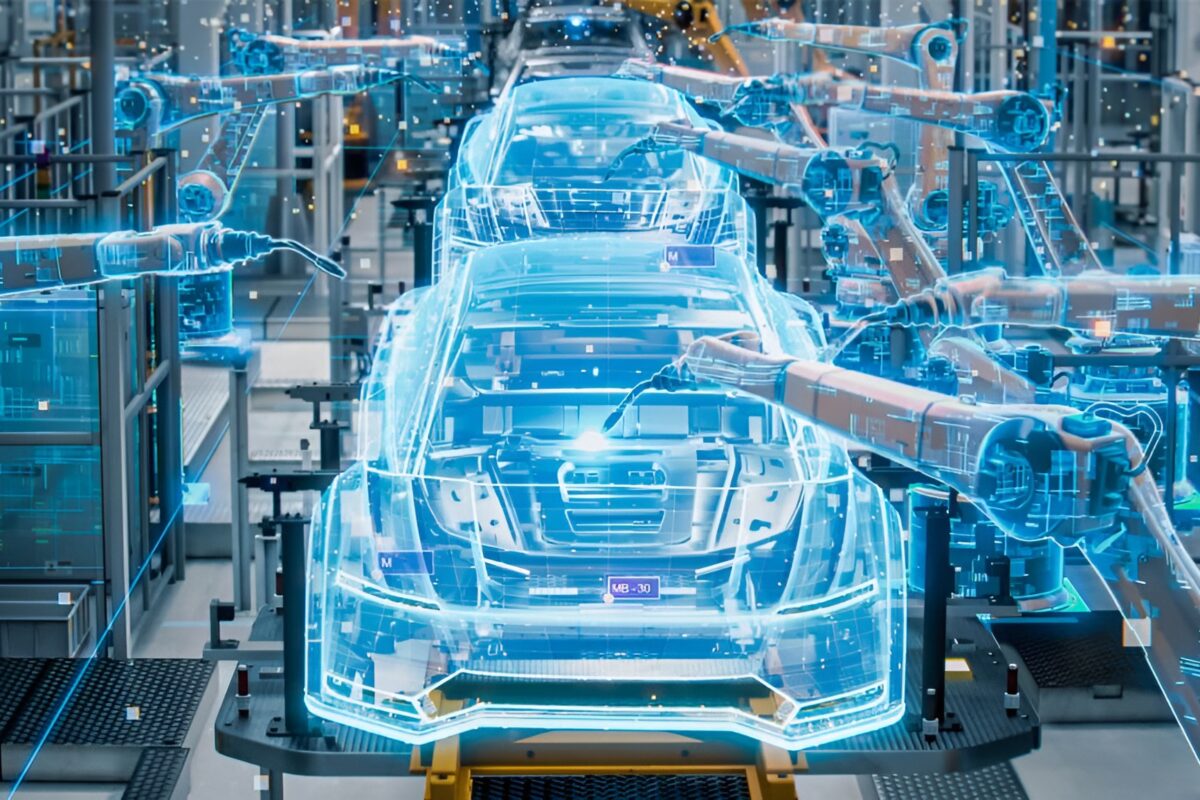
By 2025, there will be 120 billion connected devices worldwide and over 5 billion Internet users. This will enable multiple innovative applications that will change the way we live, communicate and conduct business, creating a connected world. The rapid pace of digitisation is transforming the car industry, accelerated by consumers’ evolving digital lifestyle expectations and demands for new and innovative services. All new cars will be connected by 2020; Internet-enabled, they will be a key part of the connected living market.
In the 18 months leading up to October – officially ‘national cyber security awareness’ month – we have seen an attack on a Ukraine power grid enabling the hackers to black out Western Ukraine, a sharp rise in ransomware attacks on establishments such as Hollywood Presbyterian Hospital, which paid a whopping US$17,000 ransom to regain access to files locked by ransomware, a US$81m fraudulent transfer from Bangladesh Bank and notably a massive cyber attack on TalkTalk in the UK that saw 150,000 customer details swiped; the hack cost the company £60m (US$73m) and lost it 95,000 customers. Financial results from TalkTalk show the company suffered a £15m trading impact and extra “exceptional” costs of £40m to £45m. Cyber attacks are rising exponentially – the topic featured in Frost & Sullivan’s ‘Top Trends for 2016’ and will make it firmly into the ‘Top Trends for 2017’. As a trend, cyber security is just as important now as the connectivity off which it feeds.
From the Frost & Sullivan office in central London, it has been easy in recent years to hear the familiar sound of sirens as a luxury Range Rover raced through the streets with the London Metropolitan police in hot pursuit of a vehicle just hacked and stolen from the moneyed area of Kensington. Between January and July in London alone in 2014, over 300 Range Rover Evoques and Range Rover Sports were stolen, along with 63 BMW X5s and 3 Series models. These were organised thefts; one brand new Range Rover was stolen in London and found on the Hungarian border less than 48 hours later. The car had been tracked from purchase, suggesting that as early as when it was in the showroom the theft of that vehicle was planned. As cars become ‘computers on wheels’, the hackers jump for joy. How long will it be before we see a hacked and out of control autonomous vehicle careering through London? A far scarier image than a person trying to make it to a border with a Range Rover…
As cars and information systems get heavily integrated, hackers will have more incentive to… hack
As the supply chain becomes more interconnected and fragmented, that network of suppliers is also opening itself up to threats and attacks which will in turn harm its own clients. While strong collaboration with the supplier base is critical to success, it has also weakened the OEM defence lines to external attacks. This is further exacerbated by the move to the Cloud as most OEM executives are concerned by the perceived loss of data control once it is deployed in the Cloud. The challenge here, with globalisation key to expanding into emerging markets, is that a number of OEMs are deploying Cloud-based solutions to allow local suppliers to connect into a centralised B2B hub.
Added to this is the move to the Internet of Things where smart factory, R&D efforts, logistics and supply chain and aftermarket service infrastructure will need to be connected to common back end platforms for added optimisation. This can only become more complicated.
Trends in the automotive market
When Frost & Sullivan recently researched Top-of-Mind issues troubling Connected Car Senior Management in the industry, unsurprisingly Distributed Security solutions were ranked number 1. Other areas highlighted were Over the Air updates and the creation of new revenue streams.
Data privacy and data security
Data privacy and security issues have raised their ugly heads in recent months with increasing frequency. In 2020, more than 70% of consumers are likely to consider security a key parameter when purchasing a car. Imagine a future in which a consumer is swayed between purchases over whether or not a firewall is provided as standard in a connected car? Traditional buying factors like performance could well be a secondary or tertiary option on the average customer’s expectation list.
Consumers are addicted to convenience and connectivity in their everyday lives. Consumer electronics, especially mobile phones, provide a level of convenience that cannot be offered by any other industry. Customers also have high levels of expectation when it comes to connectivity from industries other than the automotive industry.
In their rush to get cars connected, OEMs could be providing a connection to hackers that can instead be easily compromised and cost them the competitive advantage they were hoping to gain through connecting their products
Security and privacy are often taken for granted when it comes to consumer electronics. Consider, for instance, the mobile phone: consumers will accept terms and conditions from Apple or Google without batting an eyelid, and with little concern about what Google or Apple have access to when it comes to personal and private content.
Although it is frowned upon that a celebrity’s iCloud accounts may have been compromised, it rarely makes headlines. However, when eager journalists and white hat hackers remotely break into a Jeep, automotive and mainstream media buzzes with the dangers of hacking and the threat to cyber security.
Cyber security hyper concern
The emphasis though remains on cyber security advancements in an industry that quite realistically is poorly prepared to meet minimum requirements. Industry consolidation is critical to bring into the value chain the expertise that does not exist today. Intel, for example, has created an Automotive Security Review Board, a sort of Justice League of security experts to combat and address cyber security challenges. Other companies have made investments and acquisitions to strengthen their cyber security; Harman, for example, invested over US$1bn in acquiring TowerSec, Red Bend Software and Symphony Teleca. Recent experience has shown that, especially in the US, concerns around cyber threats will prompt government bodies to initiate research projects and proactively frame regulations similar to cyber security laws in other industries. The US Security and Privacy in Your Car Act (SPY Car ACT) proposes that OEMs focus on security initiatives such as data protection, data privacy and supply chain security. In 2016, the European ENISA (European Network and Information Security Agency) is to form a team of experts and start working with OEMs as well as partners to evaluate security initiatives related to connected cars and to draft security recommendations for OEMs.
As cyber security systems need to evolve, the threat against them will evolve, too. Hackers, so-called ‘hactivists’ and criminals will find new and innovative ways to attack
Recent hacks indicate that in-vehicle and wireless are major threat vectors; hackers are likely to target the weakest link and the increasing number of attack surfaces until the original threat vectors are controlled. OEMs and Tier 1 suppliers have acted on these hacks and come up with a number of initiatives and collaborative partnerships, including a collaboration between GM and Delphi; Volkswagen’s cross industry co-operation for greater cyber security in Germany (DCSO); Tesla’s engagement with white hat hackers; and the Volvo Cars collaboration with government agencies, academia and tech companies.
Frost & Sullivan has identified a number of different ways in which automotive companies will focus their efforts and investments. These include acquiring software companies; partnering with specialist security companies; providing security training; collaborating with ethical hackers; hiring security experts and restructuring the organisation; and conducting V2X field trials and taking security initiatives.
Recent hacks indicate that in-vehicle and wireless are major threat vectors; hackers are likely to target the weakest link and the increasing number of attack surfaces until the original threat vectors are controlled
Conclusions
As we race towards a connected and autonomous future, the automotive industry will increasingly become vulnerable to cyber threats and attacks. The automotive industry is dealing with a number of problems, including an explosion of data, complicated IT infrastructure and unreal customer expectations, to name but a few. None of these issues are likely to go away in the future, and at the same time no system is physically capable of solving or getting on top of them. Cyber security investments act like insurance against an attack from happening, or at least put the right measures in place to protect the business from such attacks.
As cyber security systems need to evolve, the threat against them will evolve, too. Hackers, so-called ‘hactivists’ and criminals will find new and innovative ways to attack. As cars and information systems get heavily integrated, hackers will have more incentive to… hack. Vehicle manufacturers, just as all other participants in the automotive value chain, must understand that for cyber security, there is no one-size-fits-all solution, and it definitely cannot be achieved with a onetime investment. Cyber security services need to be tailor-made for specific needs and usage and also continually upgraded along with advancements in science and technology. The current crops of ‘traditional’ automotive suppliers do not have what it takes to provide such a level of protection to OEMs. This has been underlined by the scramble to acquire expertise and bring it into the automotive fold.
The automotive industry should learn from the experience of other industries such as banking and finance, and partner with the right suppliers who know how to get the job done. In their rush to get cars connected, OEMs could be providing a connection to hackers that can instead be easily compromised and cost them the competitive advantage they were hoping to gain through connecting their products.